Introduction: Why You Need a Hash Generator 🔗
In today's digital world, data security and integrity are more important than ever. Whether you're verifying downloads, storing passwords, validating API responses, or checking file integrity, hashing plays a critical role.
However, generating hashes manually using programming languages or command-line tools can be complicated and time-consuming. That’s why a Hash Generator tool is essential for developers, security professionals, and everyday users.
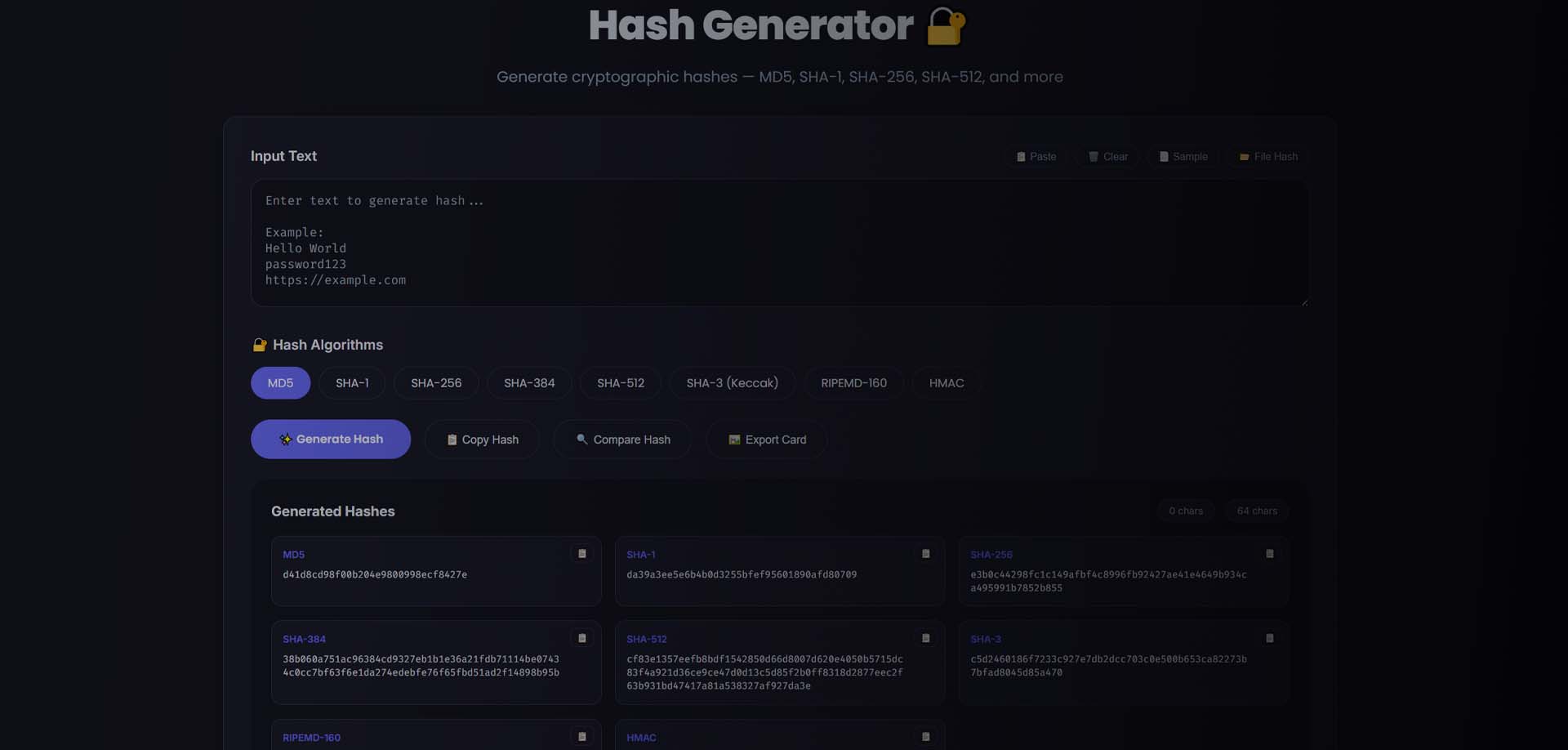
Our free online hash generator allows you to instantly create MD5, SHA-1, SHA-256, SHA-384, and SHA-512 hashes from any input text — fast, secure, and completely free.
What is a Hash Generator? 🔗
A Hash Generator is a tool that converts any input text into a fixed-length string using a cryptographic hashing algorithm. This output is called a hash value or digest.
Important properties of hashing:
- Fixed output length
- One-way function (cannot be reversed)
- Same input always produces same hash
- Tiny input change produces completely different output
- Used for security and verification
Example 🔗
Input: Hello World
SHA-256 Output: a591a6d40bf420404a011733cfb7b190d62c65bf0bcda32b57b277d9ad9f146e
Even changing Hello World to hello world generates a completely different hash.
Types of Hash Algorithms 🔗
1. MD5 Hash Generator 🔗
MD5 produces a 128-bit hash and is one of the fastest hashing algorithms.
Common Uses:
- File checksum verification
- Duplicate detection
- Non-security fingerprinting
Example: Input: password123 MD5: 482c811da5d5b4bc6d497ffa98491e38
⚠️ MD5 is not recommended for password security.
---
2. SHA-1 Hash Generator 🔗
SHA-1 produces a 160-bit hash and is more secure than MD5 but now considered outdated.
Common Uses:
- Legacy systems
- Git version control
- File fingerprinting
---
3. SHA-256 Hash Generator 🔗
SHA-256 is part of the SHA-2 family and generates a 256-bit hash.
Common Uses:
- Password hashing
- API security
- Blockchain systems
- Digital signatures
Example: Input: admin SHA-256: 8c6976e5b5410415bde908bd4dee15df...
---
4. SHA-512 Hash Generator 🔗
SHA-512 produces a 512-bit hash and offers the highest level of security.
Common Uses:
- Enterprise security
- Password storage
- Cryptographic applications
- Secure tokens
Why Use a Hash Generator? 🔗
🔐 Password Security 🔗
Websites store hashed passwords instead of plain text. This prevents attackers from reading passwords directly.
📦 File Integrity Verification 🔗
Developers publish hash values so users can verify downloads were not modified.
🧪 Data Fingerprinting 🔗
Hashes uniquely identify data without exposing the original content.
🔑 API Authentication 🔗
Hashing is used in API keys, tokens, and request signing.
⚡ Quick Data Comparison 🔗
Compare two large files using hashes instead of full content.
How to Use the Hash Generator (Step-by-Step) 🔗
Using our tool is extremely simple:
Step 1: Enter Your Text 🔗
Type or paste any string into the input box:
- Passwords
- Text
- JSON
- API keys
- File content
Step 2: Select Hash Algorithm 🔗
Choose from:
- MD5
- SHA-1
- SHA-256
- SHA-384
- SHA-512
Step 3: Generate Hash 🔗
The tool instantly creates the hash value.
Step 4: Copy Result 🔗
Click copy to use it in:
- Databases
- Code
- Security systems
- Verification checks
Common Hash Generator Use Cases 🔗
1. Password Hashing 🔗
Instead of storing: password123
Store: ef92b778bafe771e89245b89ecbc08a44a4e...
This protects user data.
---
2. File Verification 🔗
Developer provides:
File: software.zip SHA-256: d2d2d2c9f0a...
You generate hash and compare. If both match → file is safe.
---
3. API Request Signing 🔗
Hash is generated using: timestamp + secret + payload
This prevents tampering.
---
4. Data Deduplication 🔗
Same files generate same hash → remove duplicates easily.
Hash Generator vs Encryption 🔗
Many users confuse hashing with encryption.
| Feature | Hashing | Encryption | |--------|--------|------------| | Reversible | No | Yes | | One-way | Yes | No | | Used for passwords | Yes | No | | Used for storage | Yes | Yes | | Output length | Fixed | Variable |
Hashing is one-way, encryption is two-way.
Hashing Example Comparison 🔗
Input: MiniToolsPro MD5: 0f7e3f8a0f2e7a4d6a2e0...
SHA-1: 8a1d7c0b2a1e4c...
SHA-256:
0c4f32d1b2a0f7...
SHA-512:
c9d5a4e7d1a2f8...
Each algorithm produces a completely different output.
When to Use Each Hash Type 🔗
Use MD5 when:
- Speed matters
- File checksum
- Non-security usage
Use SHA-1 when:
- Legacy systems required
- Compatibility needed
Use SHA-256 when:
- Password hashing
- Secure systems
- API authentication
Use SHA-512 when:
- Maximum security required
- Enterprise applications
- Cryptographic use
Developer Use Cases 🔗
Backend Developers 🔗
- Store hashed passwords
- Generate tokens
- Secure APIs
Security Engineers 🔗
- Integrity checks
- Digital fingerprinting
- Secure hashing
DevOps Engineers 🔗
- Deployment verification
- File checksum validation
- Build integrity
Web Developers 🔗
- Session tokens
- Login security
- Cookie hashing
Hash Generator Features 🔗
Our free hash generator provides:
✅ Multiple hash algorithms ✅ Instant generation ✅ Secure processing ✅ Copy to clipboard ✅ Mobile friendly ✅ No login required ✅ Unlimited usage ✅ Developer friendly
Common Mistakes to Avoid 🔗
❌ Using MD5 for passwords ❌ Assuming hashing is encryption ❌ Comparing partial hashes ❌ Ignoring case sensitivity ❌ Hashing with extra spaces
Always ensure input text is exactly the same.
FAQ: Hash Generator 🔗
What is a hash used for? 🔗
Hashes are used for security, file verification, password storage, and data integrity.
Can hash be reversed? 🔗
No. Hashing is one-way. You cannot retrieve original data.
Why are hashes fixed length? 🔗
Hash algorithms always produce consistent output size.
Is SHA-256 secure? 🔗
Yes, SHA-256 is currently considered secure.
Which hash is best for passwords? 🔗
SHA-256 or SHA-512 (with salt) is recommended.
Is this hash generator free? 🔗
Yes, completely free with unlimited usage.
Try the Free Hash Generator 🔗
Use our free online tool to generate hashes instantly:
👉 https://minitoolspro.com/tools/hash-generator
Generate:
- MD5 Hash
- SHA-1 Hash
- SHA-256 Hash
- SHA-384 Hash
- SHA-512 Hash
Perfect for developers, security professionals, and everyday users.
Start generating secure hashes now.